Description
HouseOfHashing is a free (to use) App Inventor and compatibles extension for SHA-1 and SHA-2 hashing and HMAC (Hashed Message Authentication Codes) functions. This extension is published with a 3-Clause BSD License. Developed by ©Eric M. Kok (appsbeheerder).
Extension current version
Version: V2
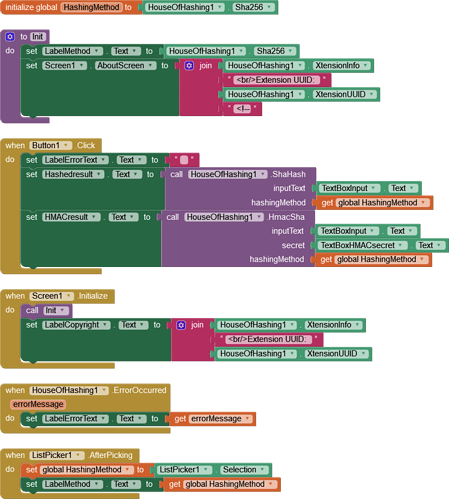
Example App
Introduction
SHA (Secure Hash Algorithm) is a family of cryptographic hash functions, widely used in security protocols and applications. They take an input (or ‘message’) and return a string of bytes (called a ‘digest’) that is unique for each unique input. Changes to the input, even minor ones, will produce a totally different output.
HMAC (Hash-based Message Authentication Code) is a specific type of Message Authentication Code (MAC) involving a cryptographic hash function (such as SHA-256) and a secret cryptographic key. It’s used to verify both the data integrity and the authenticity of a message at the same time.
SHA and HMAC are used for data integrity to ensure that the data sent over network(s) has not been tampered with. The sender generates and sends a hash of the message along with the message itself. The receiver calculates a hash from the received message and compares it with the received hash. If they match, the message has not been tampered with.
The reason these methods can be used without exchanging keys is that the hash functions themselves do not require a key. HMAC does require a key, but this key is known only to the sender and receiver and is not transmitted with the message. This makes it very difficult for an attacker to modify the message or hash without knowing the secret key.
Since there was not a full set of SHA hashing and HMAC functions in one extension available, I developed the extension.
Remember: SHA and HMAC do not provide encryption itself but checking data integrity and authenticity only!
Functions
ShaHash
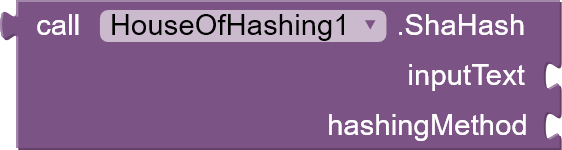
Computes the hash of the input text using a specified hashing method.
Parameters
inputText: The input text to be hashed.hashingMethod: The hashing method to be used (Sha1, Sha224, Sha256, Sha384, or Sha512).
Returns
The hash result in hexadecimal format.
HmacSha

Computes HMAC (Hash-based Message Authentication Code) for the given input text using a secret key and a specified hashing method.
Parameters
inputText: The input text to be hashed.secret: The secret key for HMAC.hashingMethod: The hashing method to be used (Sha1, Sha224, Sha256, Sha384, or Sha512).
Returns
The HMAC result in hexadecimal format.
Hashing Method Properties
Choose the hashing method.
Sha1, Sha224, Sha256, Sha384, Sha512
![]()
![]()
![]()
![]()
![]()
REMEMBER Use SHA256 or higher because lower versions, SHA1 and SHA224, have proven to be vunerable to attacks. But for legacy reasons they are kept.
XtensionInfo
![]()
Property to get information about the extension (name, version, copyrights).
XtensionUUID
![]()
Property to get the extension UUID.
Events
ErrorOccurred
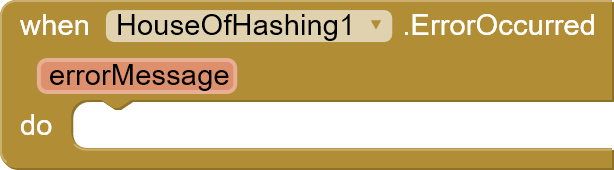
Event triggered when an error occurs.
Parameters
errorMessage: The error message.
Android Supported API Levels
Hashing name -> Supported (API Levels)
SHA-1 -> 1+
SHA-224 -> 1–8,22+
SHA-256 -> 1+
SHA-384 -> 1+
SHA-512 -> 1+
Except for SHA224, no specific Android version needed*
*source: MessageDigest | Android Developers
Downloads and updates
HouseOfHashing extension downloads and updates can be found at the https://codeberg.org/appsbeheerder/HouseOfHashing. Make sure to check for updates and additional information at the repository.
Example App blocks
Extension UUID
56f13b25-3ce1-4e41-9094-85c89faf59b1
Copyrights & License
-
 Eric M. Kok (appsbeheerder)
Eric M. Kok (appsbeheerder)
For the extension, which is compiled Java source, the The 3-Clause BSD License is applicable.The 3-Clause BSD License
Copyright 2023 Eric M. Kok (appsbeheerder)Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
- Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer.
- Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution.
- Neither the name of the copyright holder nor the names of its contributors may be used to endorse or promote products derived from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS" AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
Donating

A lot of work is put in this extension and the documentation. Support me for more work on extensions.
Donate me at https://paypal.me/ericdemagier
MIT Appathon use of extension
- You are allowed to use the .aix (jar) extension HouseOfHashing, as part of an MIT Appathon app. https://appathon.appinventor.mit.edu/